In the age of information, the digital footprints we leave across the internet are meticulously gathered and analyzed by leading companies, all in pursuit of targeting and monetizing user behaviors. For this reason, data sharing comes with inherent risks. Every click, every message, every transaction traversing the web faces the threat of interception by hackers or other malicious third party entities. Thus, ensuring our digital privacy is now more important than ever.
End-to-end encryption is a method that can be used to securely exchange data on the internet. In this practice users can encrypt their data at the source, such that only intended recipients possess the keys to decrypt it. But what exactly is end-to-end encryption, and how can you integrate it into your digital arsenal? In this post, we tackle the essence of end-to-end encryption, explaining its complexities and guiding you through its implementation.
Firstly, let us understand what encryption is since this is the basis of end-to-end encryption. Using data encryption is a way to protect your data as it will be encoded in an unreadable form wherein only the user with the corresponding decryption key can decipher and access it. As the encrypted data passes through the Internet Service Provider (ISP), other entities will not be able to access the information as it appears unreadable to them.
By encrypting data or transforming it into an unreadable data, the user is protected from unwanted sharing of information. This method is widely applied to preserve the integrity of data in transferring files, messages, documents, and other forms of communication of a network.
Encryption works in a way such that you put your data into a secret code before sending it off into your ISP. This process involves using an encryption algorithm, which is basically a set of rules for scrambling the data. There are various encryption algorithms available, each offering different levels of security.
Once you've picked the right encryption algorithm, you also need an encryption key, which is like a secret password. Together, the algorithm and key work their magic, transforming your original data into an encrypted form. This encrypted data can then be safely transmitted to your recipient through the network or your chosen communication channel.
Now, here's the beauty of encryption: even if someone intercepts your encrypted data as it travels across the network, they won't be able to make sense of it without the decryption key. It's like trying to read a secret message without knowing the secret code. Only the intended recipient, armed with the decryption key, can unlock the encrypted data and reveal the original information in its readable form.
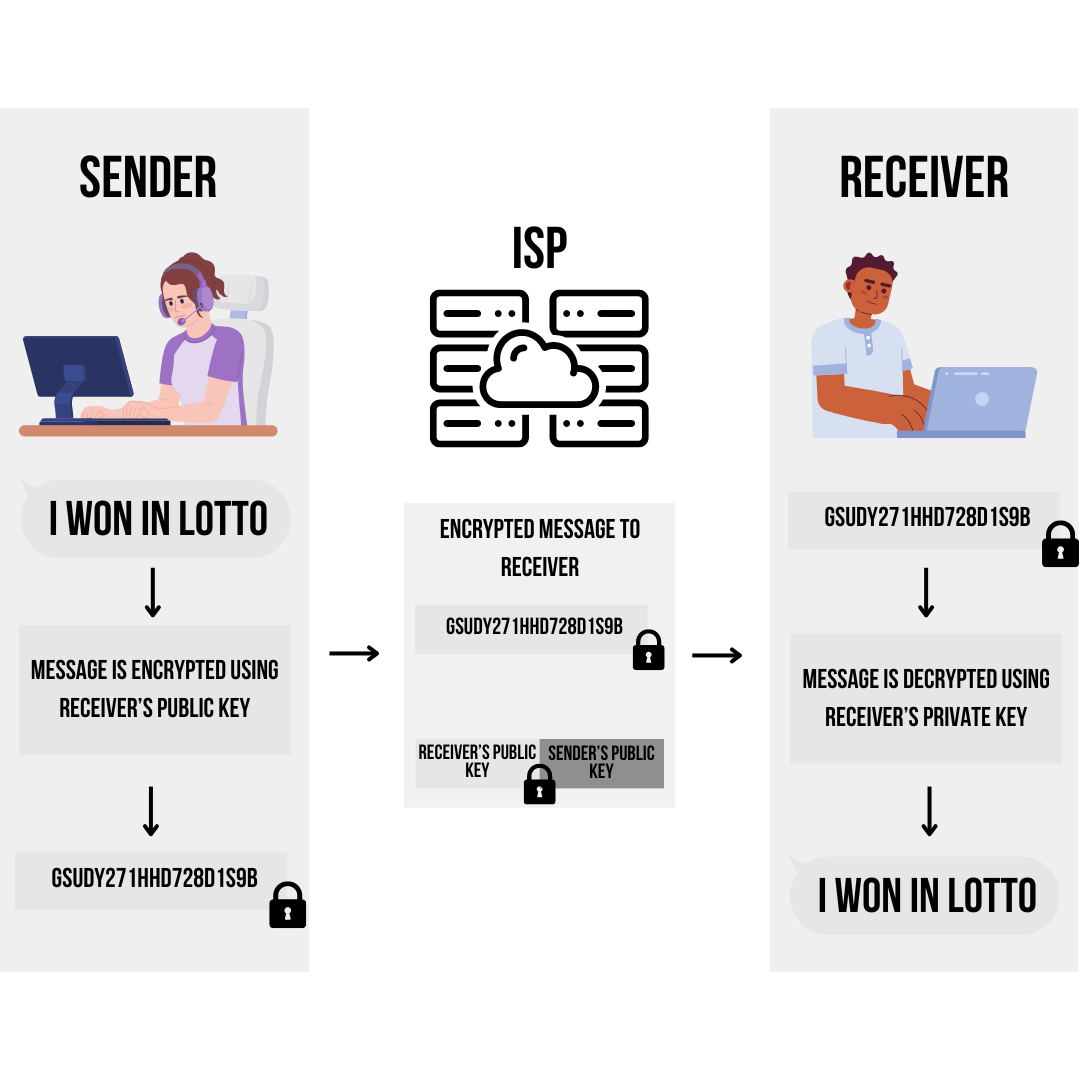
As mentioned above, there are numerous encryption algorithms or kinds of encryption but in this post, we will only be focusing on the encryption with the use of paired public and private keys (asymmetric public key) as this is the type of encryption used by an end-to-end encryption. As its name suggests, the data is only encrypted at the end points which are the sender and the receiver. Therefore, by using a pair of public and private keys, the data can be transmitted from end-to-end without any interference as outside entities will not be able to read or understand the data.
Refer to the image below for a visualization of how end-to-end encryption works. It starts with the data from the sender. Then, this data is encrypted using the public key of the receiver. After the data is encrypted it can be safely transmitted to the network or ISPs. When the receiver gets the message, it will need to use its private key to decrypt the message. Only after then will the receiver be able to read the message of the sender.
The implementation of End-to-End Encryption requires understanding of the following terms so a brief definition is provided correspondingly:
Encryption Protocol - These are the protocols wherein encryption algorithms are subject to. There are various types of encryption protocols with corresponding functions like TLS/SSL for communications or use of SSH for remote connections to computers.
Public and Private keys - Public and private keys are used in pairs for end-to-end encryption. The public key is openly available to all system users, while the private key remains securely confined to the user's device, serving as the exclusive means for decrypting data.
Asymmetric Encryption - This is the type of encryption used when implementing end-to-end encryption. In this encryption a combination of public key and private key is used to ensure that the data is transmitted without any interceptions.
Here are the steps than you need to follow to implement end-to-end encryption:
messaging applications like Messenger, WhatsApp, etc., use or have a feature that uses end-to-end encryption. With this, when a user sends a message it can not be intercepted. However, it is important to note that most channels of communications do not automatically enable end-to-end encryption. In this case, data shared in your conversation are susceptible to being intercepted by malicious entities.
Online banking either through a website or an app uses end-to-end encryption. Therefore, all the data you send and receive such as your bank balance, expenses, and other transactions are not visible to any other person or entities. This is necessary as financial transactions primarily involve sensitive information.
Online Shopping: Almost everyone shops online nowadays and this means sensitive data like your bank information, address, contact number, etc. are shared through these platforms. The use of end-to-end encryption is crucial in ensuring that none of these get leaked to hackers and other entities.
Most of our files are uploaded in the cloud be it through iCloud Drive, Google Drive, Dropbox, etc.,and all of these need to be stored with confidentiality. Thus, end-to-end encryption is used so that every time you upload or download a file from the cloud, you can be free of worry that it will be intercepted or reproduced without your consent.
Nowadays, there are healthcare transactions carried out online as the use of telemedicine becomes more popular. A patient’s information and all of the records stored by healthcare providers is sensitive and should not be accessible by other entities. Thus, end-to-end encryption is used in transactions that involves any of these sensitive data or records.
The most obvious advantage of using end-to-end encryption is the heightened security that it provides to your privacy. By ensuring that only intended recipients get access to your information, you can be assured that your privacy is not compromised. This leads to the possibility of exchanging sensitive information online. Online banking, shopping would not have been possible if end-to-end encryption was not discovered and popularized. We can only confidently transact online using our real life money because we know that our information is protected by some digital security. End-to-end encryption is the backbone of the security in most of these online transactions.
Aside from the data that we share, the data that we access is also protected by end-to-end encryption. There are instances where we receive and download information, files, and other data from other users. If these are sensitive information, we must ensure that it is not altered or tampered with during the communication process. Therefore, use of end-to-end encryption is also necessary for maintaining the integrity of data.
Finally, possibly the most important use of end-to-end encryption is to avoid massive cyber attacks. If sensitive data is breached as it is highly possible without using end-to-end encryption, then hackers and other malicious actors could penetrate the system of a company per say and this could lead to damage of information and other ways of compromising users’ safety and privacy.
The use of end-to-end transactions can be complicated as there is softwares and algorithms involved.It can delay processes or make it more challenging especially when processes involve accessing the encrypted data. This is primarily concerning for law enforcement agencies, even they can not access any data that is encrypted unless they are the intended recipient. Thus, in obtaining and analyzing evidence, an end-to-end encryption sort of blocks their way. Additionally, it requires secure handling of the encryption keys because if these are lost then it will be impossible to retrieve the data encrypted.
Moreover, even if end-to-end encryption secures transactions, it does not completely guarantee your protection. Since end-to-end encryption only encrypts the data up until it is decrypted by the receiver, then any problems on the receiving end still poses danger to the security of your data. Therefore, it is still important to ensure the reliability of both ends.
The discovery of end-to-end encryption is one of the most significant breakthroughs in cyber security. It allows safer communication by ensuring that during transactions using an end-to-end encryption, the shared information will not be accessible and can not be intercepted by other parties. Providing this kind of security made most of the significant online transactions possible. Our lives are now made easier as we can do online communication, online banking, online shopping, storing of files in the cloud, and even seeking professional healthcare help online. We can only do all of these because end-to-end encryption is implemented for these transactions. It is also possible to implement end-to-end encryption by yourself. A general set of instructions have been provided as your guide on how you can do this.
Implementing end-to-end encryption can provide you with security, specifically in ensuring that your data is protected from end-to-end of transactions. However, using end-to-end encryption does not guarantee that your privacy will not be compromised as it is still subject to limitations. Therefore, end-to-end encryption must be used in conjunction with cyber security practices to ensure that your privacy will not be compromised.